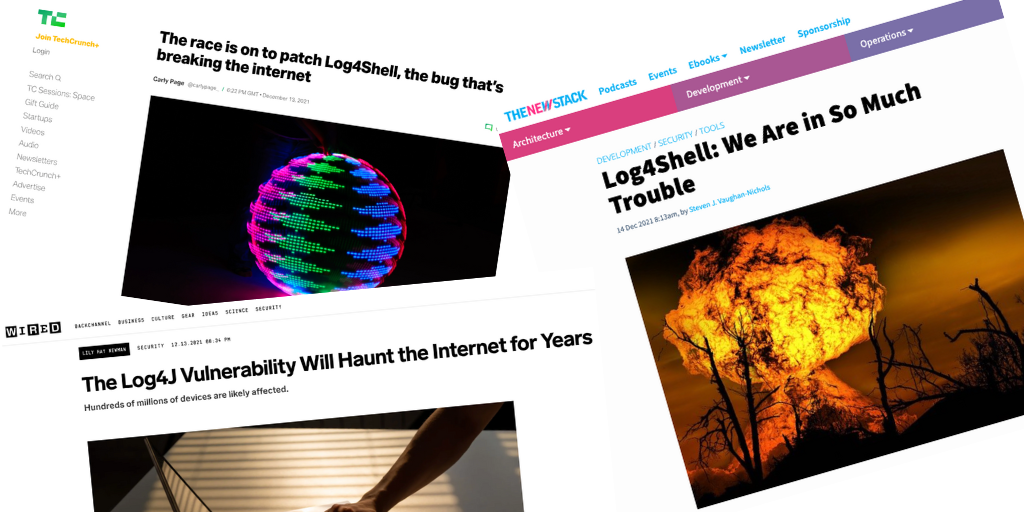
Like many news outlets and security companies, you will have seen that a severe vulnerability was discovered on Thursday 9th December 2021. It has a devastating effect on systems across the internet. The severity of this particular vulnerability is rated 10/10, the highest known to memory. This means that hackers can remotely obtain unauthorised full access to the vulnerable system with zero user interaction.
A zero-day vulnerability is a weakness within an IT system or device that has been disclosed but has not yet been patched. Zero-day vulnerabilities are discovered before security researchers are aware of their existence, meaning cybercriminals race to exploit (take advantage of) these zero-day vulnerabilities, which is known as a zero-day exploit. Log4j is classed as a zero-day.
What is Log4j?
Log4j is a commonly used Java logging library that has been developed by the Apache Foundation. Java is a well-known computer programming language that emerged in the 90s. Similar to all programming languages Java libraries are useful pieces of code written by someone else to help the development community.
Log4j is a library that is used by developers worldwide, because of its ability to keep track of what happens in software applications and cloud services, in which the data tracked is then stored in a log file. In computing, a log file is a file that contains information about activities, events, and operations that take place within a computer system or network, data that is useful to identify patterns. Hundreds of millions of devices, servers, and cloud services use this java package, which is the reason why the vulnerability found within this software is so critical.
How serious is the Log4j Vulnerability?
To put it plainly, this vulnerability is critical. The number of users for Log4j plus the potential impact of the security flaw makes this not only extremely high risk but also extremely dangerous, giving it a vulnerability score (CVSS) of 10/10.
Who is affected by Log4j?
Everyone, including organisations and individuals, is at risk. Individuals can be affected indirectly because cybercriminals can use the security flaw to install malware (malicious code) and backdoors onto servers and other computer systems, meaning that when these types of services are impacted maliciously, many millions of users will also become affected.
Businesses should also be aware of the potential consequences if their IT systems were to be exploited because of the zero-day vulnerability: cost of incident response, harmful impact to their reputation and brand image, and other financial losses.
At the North West Cyber Resilience Centre we're here to help, don't hesitate to contact us if your organisation wants to be better protected this holiday season or in 2022.